
Chapter Two Tokenomics is not Economics the WAMNET
In Chapter One we established a few things, such as,
- In just a few months, globally, in just about every sector customer loyalty will be up for grabs
- Customer experience is the challenge of the recovery
- W3 CX solves a few things, and those things start with the network
- But not the network we have today It all starts with a smart network

Next, we will describe in detail, this smart network, as we introduce the WAMNET, a Wireless, Autonomous, Massive Network, using alternative persistent DNS, and persistent storage. WAMNET’s are created by miners who collect economic rent on this platform. This is not the same network you use to access MySpace.
This is more of a platform, and platforms provide value, members access this value using utility tokens, and they access this value in a peer-to-peer environment becoming known as W3.
Members access value that is native to the platform, and sometimes, available at zero marginal cost. For instance, Digital CX Platform As A Service, Imputed KYC, AML, or Proof of Identity (POI), rural infrastructure for digital freelancing (GPD for recovery), Gain company assets through Federal Grants, Infrastructure for renewable energy, autonomous transportation, and Global, peer-to-peer commerce.
Whew! Catch my breath here, that was a mouth full! But First some definitions
Customer Centricity in the Platform Revolution | Sangeet Paul Choudary
In his 2016 keynote, he discusses the shift from asset-centric business models to consumer-centric platform business models. From Pipes to Platforms.
Named Data Networking (NDN) – Named Data Networking is a Future Internet Architecture research project supported by the National Science Foundation, which has received over $13.5M in funding from NSF from 2010-2016.
UCLA Professor and Jonathan B. Postel Chair in Computer Science Lixia Zhang leads the project along with Internet Hall of Fame inductee and UCLA adjunct professor Van Jacobson.
Van Jacobson is an American computer scientist, renowned for his work on TCP/IP network performance and scaling. He is one of the primary contributors to the TCP/IP protocol stack—the technological foundation of today’s Internet. Wikipedia
The NDN project is developing a new fundamental architecture for the global Internet that leverages thirty years of empirical evidence of what has worked (and what has not). It aims to provide a practically deployable set of protocols replacing TCP/IP that increases network trustworthiness and security, addresses the growing bandwidth requirements of modern content, and simplifies the creation of sophisticated distributed applications.
Workshop on Named Data Networking (NDN) at NIST, 2016
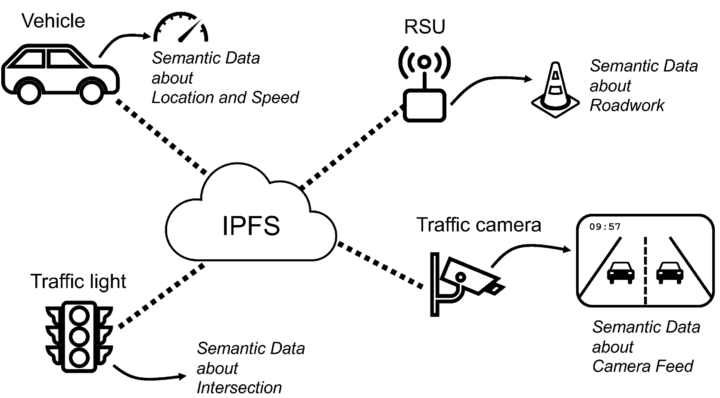
The Inter Planetary File System – IPFS, https://ipfs.tech/ – IPFS powers the creation of diversely resilient networks that enable persistent availability — with or without internet backbone connectivity. This means better connectivity for the developing world, during natural disasters, or just when you’re on flaky coffee shop wi-fi.
IPFS is a DNS replacement that finds information by its contents, not its location this is called content addressing (Kinda like Named Data Networking, but still different). With IPFS, you don’t just download files to network storage, IPFS also helps distribute them. When your friend a few blocks away needs the same Wikipedia page, they might be as likely to get it from you as they would from your neighbor or anyone else using IPFS (Napster except much more disruptive to more industries).
LDNS, https://www.nlnetlabs.nl/projects/ldns/about/LDNS is a DNS library that facilitates DNS tool programming. Translations in LDNS can come from any database. Even a distributed ledger database (Blockchain). If you use a permanent, distributed ledger database to record your DNS, you have persistent Lifetime DNS, when the payment is made to record it, then that’s it, no payments for a lifetime. Domain Registrars like Go Daddy, have become so 1990s.
And you can use multiple storage mediums to store a single document, which can only be assembled through your LDNS instance which may only be in a single node. Security is built into the platform. Node communications are all encrypted and Quantum Resistant.
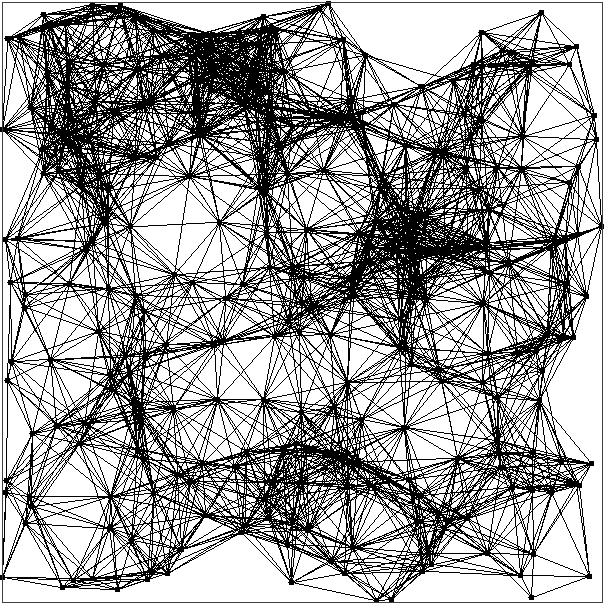
Mesh Network A mesh network is a local area network topology in which the infrastructure nodes (i.e. bridges, switches, and other infrastructure devices) connect directly, dynamically, and non-hierarchically to as many other nodes as possible and cooperate to efficiently route data to and from clients.
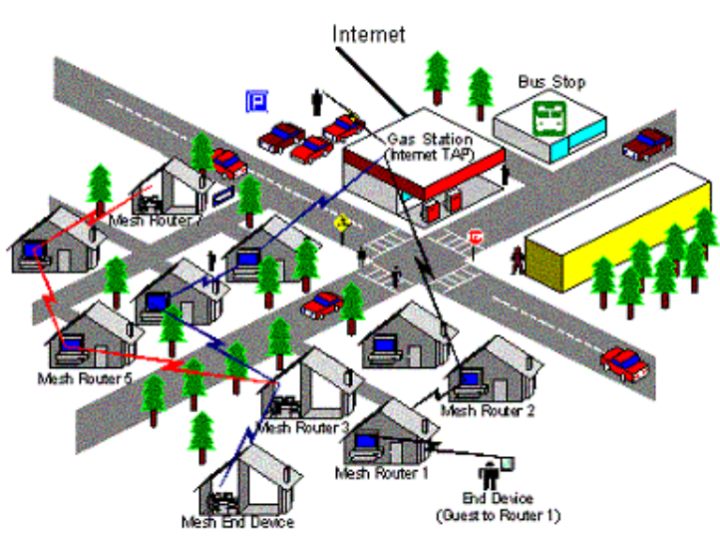
This lack of dependency on one node allows for every node to participate in the relay of information. Mesh networks dynamically self-organize and self-configure, which can reduce installation overhead. The ability to self-configure enables the dynamic distribution of workloads, particularly in the event a few nodes should fail. This in turn contributes to fault tolerance and reduced maintenance costs.
Zero-knowledge proof – In cryptography, a zero-knowledge proof or zero-knowledge protocol is a method by which one party (the prover) can prove to another party (the verifier) that a given statement is true while the prover avoids conveying any additional information apart from the fact that the statement is indeed true. The essence of zero-knowledge proofs is that it is trivial to prove that one possesses knowledge of certain information by simply revealing it; the challenge is to prove such possession without revealing the information itself or any additional information.
Content Delivery Network (CDN) – A content delivery network (CDN) refers to a geographically distributed group of servers that work together to provide fast delivery of Internet content.
A CDN allows for the quick transfer of assets needed for loading Internet content including HTML pages, javascript files, stylesheets, images, and videos. The popularity of CDN services continues to grow, and today the majority of web traffic is served through CDNs, including traffic from major sites like Facebook, Netflix, and Amazon.
A properly configured CDN may also help protect websites against some common malicious attacks, such as Distributed Denial of Service (DDOS) attacks.
LTE-4, Mobile Data, LTE-5, In telecommunications, Long-Term Evolution is a standard for wireless broadband communication for mobile devices and data terminals, based on the GSM/EDGE and UMTS/HSPA technologies. It increases the capacity and speed using a different radio interface together with core network improvements. The LTE data structure remains consistent Globally. We leverage the Catagory 18 LTE modem’s LTE data access capabilities. The modem is available on the Jungle website. They are carrier specific, and if your carrier goes down, your down. There are carrier fallback options that deliver 3 or 4 carrier options, which if one goes down, moves to the next (automatic failover). These options are currently providing fiber speeds (1 gig or better) for 50 cents a gig. Miners sell that bandwidth for 1 dollar a gig (50% margins).
One Tri Carrier option is TriFiWireless.com. For $279.00 plus shipping, you can buy the LTE 4 to Wi-Fi modems. You need 2 to start a Platform. The Tri-Fi units also have SDN. In most cases where cellular reception is very good, these devices provide over 1 gig of mobile data connectivity speeds. Just Plug them in and you are good to go. Sometimes we might need to augment the signal with an antenna. Most often we can estimate requirements using Google Earth.
An intelligent eSIM platform goes beyond the initial SIM activation. Its primarily used to manage a device and customize variables that greatly enhance an IoT device operator’s control of a subscriber over the long term. The key difference between a standard eSIM platform and an intelligent eSIM platform starts with the concept of “control”. That is the ability for device operators to determine how and where they get connected for the duration of a device’s lifespan.
Access more networks (i.e. AT&T, T-Mobile, and Verizon in the US)
Access more network types (i.e. 3G, 4G, 5G, NB-IoT, CAT-M)
Access more device types (i.e. devices that take a standard SIM or embedded SIM)
Seamlessly deploy devices in more countries around the world
Control devices over the long term with enhanced feature sets
Distributed computing security “Can it be secure?”
In the distributed environment, when the system is connected to a network, and the operating system firewall is active, it will take care of all the authentication and access control requests. There are several traditional cryptographic approaches that implement authentication and access control. The encryption algorithms such as Rijndael, RSA, A3, and A5 are used for providing data secrecy. Some of the key distribution techniques such as Diffie Hellman key exchange for symmetric key and random key generation (LCG) technique is used in red-black tree traversal which provides the security of the digital contents.
You can use pFsence for routing, there is a community version that is open-source and free. Secure networks start here.™ With thousands of enterprises using pfSense® software, it is rapidly becoming the world’s most trusted open-source network security solution. Get Started Now
ChatGPT: Optimizing Language Models for Dialogue – We’ve trained a model called ChatGPT which interacts in a conversational way. The dialogue format makes it possible for ChatGPT to answer followup questions, admit its m istakes, challenge incorrect premises, and reject inappropriate requests. ChatGPT is a sibling model to InstructGPT, which is trained to follow an instruction in a prompt and provide a detailed response.
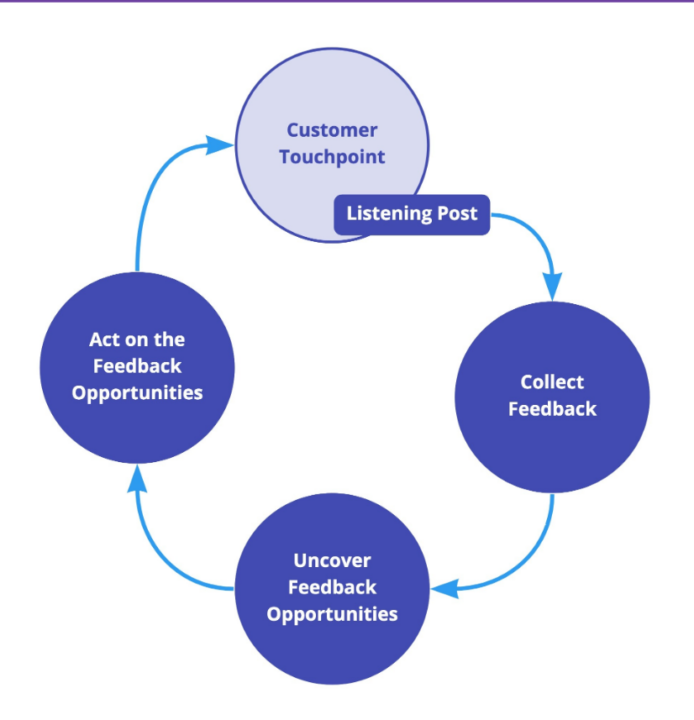
Customer Experience (CX) The 3 main components of customer experience.
- Discovery. How companies contact customers and how they make that contact relevant and meaningful
- Engagement. How customers initially interact with the company or company products.
- Delivery. How the company handles fulfillment.
The technology supporting human interaction must be seamless and unobtrusive across platforms. By knowing when and where to automate touchpoints and balancing digital with human elements, service & experience leaders can facilitate frictionless digital experiences for their customers.
World-class CX cannot be achieved without an extensive, modernized process for collecting, analyzing & utilizing data (feedback loop). From executing Voice of the Customer programs to leveraging AI & Data Analytics, holistic data-driven strategies will hold the key to the success (spoiler alert, the feedback loop).
Alright, now finally Chapter two the WAMNET –
Web3 is decentralized. And it is Distributed as well. Nodes on your network are distributed and use technology, like IPFS, and LDNS.
Nodes are local, and owned by the miners. The miners provide W3 services to the platform, and collect economic rents when members use the platform
What services you are asking?
We can start with,
Persistent Lifetime DNS – Multiple ways to do this –
Network Security – This is a Distributed Network –
Know your customer, Anti Money Laundering, Proof of Identity as a Service –
Nodes can connect to verify the single instance of an identity network-wide, which provides proof of identity (POI).
With POI comes imputed KYC and AML. KYC, AML, as a service (KYC,AML,AAS) –
In network, Legal, Regulated peer-to-peer trading of Securities, Automobiles, Homes, Digital Assets, NFT, Payroll, Payments, and anything that can be digitized (NFT, Digital Twin)
Peer to Peer, Member to Member. – services provided at near Zero Marginal cost to the platform –
Transportation in network provided by Autonomous Transportation tracked on the network (Lease a Tesla) – Basically Zero Marginal Cost Transportation.
Access to shelter and food, immediate settlement both ways, and at Zero Marginal cost to the platform.
Spoiler alert – When you apply this to Medical Campuses things change immediately.
We will cover this later in the book.
Network – Wireless AdHock Massive Network (WAMNET)
Digital Assets Embedded in Nodes (Distributed)
Nodes are AdHock and member-created and curated
Node provides data at 1 dollar a gig to members (50% margin)
Equipment – Off-shelf Long-Term Evolution (LTE) modem
MIMO 4×4 antenna
pFsense community edition Gateway
SAN devices
IPFS Nodes
LDNS Nodes
Nodes can be interconnected via encrypted node-to-node connections.
Node operators become the miners in this paradigm. They charge 1 dollar a gig for access to the network data, which includes a tunnel to the outside internet. Assets served in the node, or brought into the node are published and served (often at zero marginal cost) for 1.00 per gig, add Hoch, across the platform, and outside mobile data is provided, for 1.00 a gig in a network, similar to maybe Hologram, iota, Google Cloud IoT Core, and others.
Since this is an AdHock network, nodes connected directly to one another can exchange digital assets, outside of the traditional HTTP protocol and network, and therefore an alternative DNS could be employed here. The DNS could be persistent, and the DNS database could be persistent.
If a network has a purpose and a place, you can add value to your network. Add value to your network and it becomes a platform or a “network of networks”.
Platform=Network of Networks
Successful Platforms= Network of Networks with a Place and a Purpose
In this way, members find value in the platform, and other platform participants, provide that value member-to-member or peer-to-peer.
Platforms are probably multiple networks providing hyper-relevant value to their membership.
Platforms solve relevant social issues and supply social proof at near-zero marginal cost. Along with Persistent Lifetime DNS, Network Security, KYC, AML, as a service (KYC, AML, AAS), In network, Legal, and Regulated peer-to-peer transactions, immediate settlement both ways – Arbatrage might be a condition of membership might not. And platforms scale without any investment from the platform. W3 platforms benefit from a positive feedback loop which amplifies these ecosystems further. At Zero Marginal cost to the platform, which Brings Value to Membership.
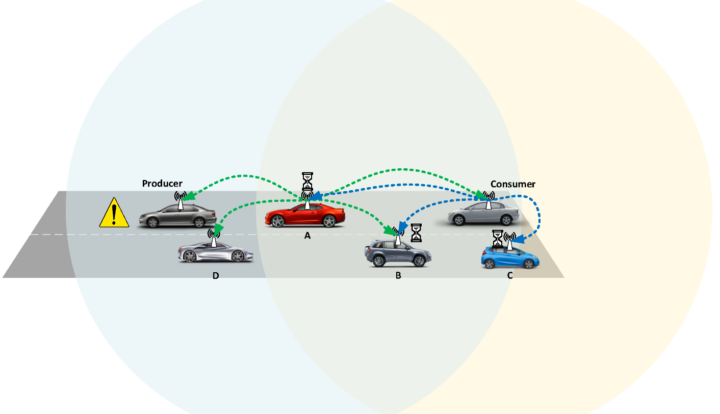
This was described in 2019 when wireless communication technologies were enabling pervasive connectivity between objects.
Internet of Things (IoT) Lab, Department of Engineering and Architecture, University of Parma, Parco Area delle Scienze 181/A, 43124 Parma, Italy
- Author Future Internet 2019, 11(4), 99; https://doi.org/10.3390/fi11040099
These communication systems, involved in the so-called “network of networks” Internet of Things (IoT), will eventually allow humans to interact with billions of devices, including sensors, actuators, services, and other connected objects, in an Internet-like way, with a forecast of more than 40 billion connected (with short-range radio communication technologies) “things” by 2022 [1] (and more than 125 billion by 2030 [2]), and more than 2.7 billion Low Power Wide Area Network (LPWAN) connections by 2029 [3].
In this context, connected things are generally defined as Smart Objects (SOs) and, thanks to the IoT, dynamically integrated into several scenarios, such as smart industries, smart cities, smart agriculture, smart health, etc. Each application area has specific requirements to be taken into account, thus having implications for the communication technologies to be considered and, possibly, adopted. In particular, IoT-related wireless technologies developed in recent years are extremely heterogeneous in terms of protocols, performance, reliability, latency, cost-effectiveness, and coverage.
For instance, some of them are designed for short-range radio communications (e.g., Bluetooth and ZigBee), others are more suitable to cover wide areas with very small bandwidth (e.g., Sub-GHz), while others are designed for middle-range communications and high transmission rate (e.g., IEEE 802.11). Moreover, IoT network topologies are generally star- or tree-based, with data collected by groups of sensors and sent to a central collector or border router, to guarantee centralized processing.
The emerging and constantly evolving IoT applications require more complex network topologies, without a predefined hierarchy but can dynamically adapt themselves to changing conditions. For this reason, there is a strong academic and industrial interest in the development of hardware and protocols able to support Wireless Mesh Networks (WMNs).
In mesh topologies, network nodes are directly and dynamically connected in a non-hierarchical way, thus allowing many-to-many communications (among nodes cooperating) to efficiently route data from a generic source to a generic destination.
In fact, in a WMN each node composing the network can operate both as a host and as a router, relaying packets sent by other nodes when the destination is not in the visibility range of the source. Moreover, mesh networks do not require infrastructure, since they dynamically self-organize and configure themselves, with consequent relevant advantages, in terms of (i) deployment, installation, and maintenance’s overhead and cost reduction; (ii) dynamic workload distribution; (iii) better reaction to node failures; and (iv) easy network topology modification.
The organization of a WMN is generally handled through the definition of a routing policy shared among all nodes, aiming at discovering and determining the best routes, based on different metrics (e.g., throughput, link quality, hops number, etc.) measured on data streams. Therefore, streams of data in WMNs cross all nodes connecting the source and the destination.
Mesh topologies are thus the most attractive alternative to traditional centralized or tree-based network topologies, where nodes are directly linked to a small subset of other nodes and the links between these infrastructure neighbors are hierarchically organized. While star- and tree-oriented topologies are very well established, highly standardized, and vendor-neutral, in the case of mesh networks the research community and vendors have not yet all agreed on common standards, with the interoperability among devices from different vendors seldom assured. Moreover, comprehensive surveys on available options in the field of mesh networks for IoT are lacking in the literature.
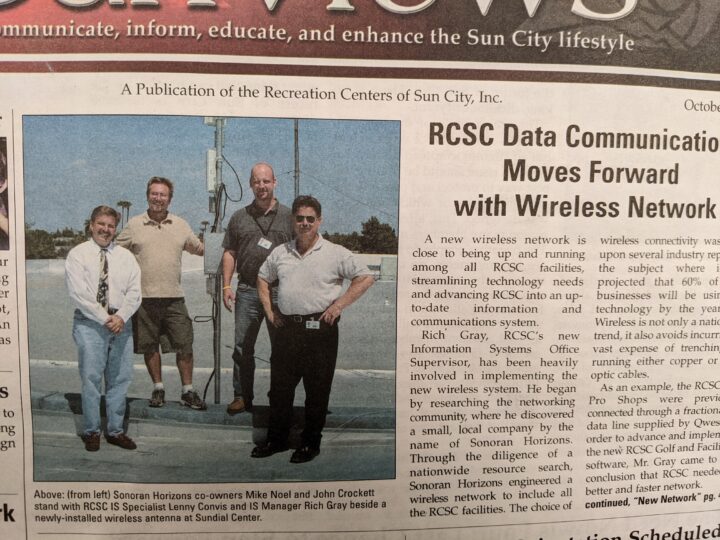
That said, I have been building out these mesh networks for a few decades now, for instance in 2005 we built a mesh network connecting all of the golf courses in sun city Arizona to the main server in the main office. This was a 10-square-mile Mesh topography supporting e-commerce in 2005. We had done several others, with projects going back to the 90″s.
And remember,
Platform=Network of Networks
Successful Platforms= Network of Networks with a Place and a Purpose
If a network has a purpose and a place, you can add value to your network. Add value to your network and it becomes a platform. Adding value generally happens when a workflow, is matched to a network.
I will use the use cases mentioned earlier in this document to illustrate this process. Next, up, Use Cases – First Use Case – Chapter 3 Use Cases – EchoTours.Travel
Be sure to follow or subscribe so I can let you know when I publish the next in the series.
Social Media – Please Connect at –
linkedin.com/in/MichaelNoel –
https://BizBuilderMike.com –
youtube.com/@BlockchainWeekly –
https://Twitter.com/BizBuilderMike –
https://www.patreon.com/BizBuilderMike
How can I help?
– Michael Noel
eschew obfuscation, espouse elucidation